Anthropic releases new AI-powered orchestration layer integrating multiple financial data providers, challenging Bloomberg’s UI moat and impacting industry workflows.
The Latest
The Orchestration Layer Arrives: What Anthropic’s Finance Agents Mean for Bloomberg, FactSet, and Wall Street
The Bubble Is Not in Valuations: It’s in the Productivity Gap
Analysis of recent data shows AI’s productivity gains are modest, revealing a structural bubble in expectations rather than asset valuations.
The NVIDIA Earnings Preview: What Q1 FY27 Will Reveal About the AI Cycle
Ahead of NVIDIA’s May 20 earnings report, this analysis explores what the Q1 FY27 results will reveal about the AI infrastructure and market demand.
The Google I/O 2026 Preview: What May 19-20 Will Reveal About Google’s Agentic Bet
Google’s I/O 2026 event on May 19-20 is set to reveal major updates on its agentic AI platform, including Gemini 4.0 and multi-agent protocols, shaping the future of AI deployment.
The Anthropic-Blackstone-Goldman JV: Reverse-Engineering the $1.5B Enterprise AI Services Structure
Anthropic, Blackstone, H&F, and Goldman Sachs form a new $1.5 billion standalone AI enterprise services company targeting mid-sized firms, announced May 4, 2026.
Forward-Deployed: The Integration Wall, and the Role That Now Pays $700K to Climb It
FDEs now command up to $700K in total compensation, becoming the highest-paid IC role in tech as they bridge enterprise AI deployment gaps.
The Memento Constraint: Why Continual Learning Is the Trillion-Dollar Bottleneck Nobody Is Pricing
A16z highlights the ‘Memento Constraint’ in AI, revealing that current models can’t learn across conversations, posing a major bottleneck for enterprise AI growth.
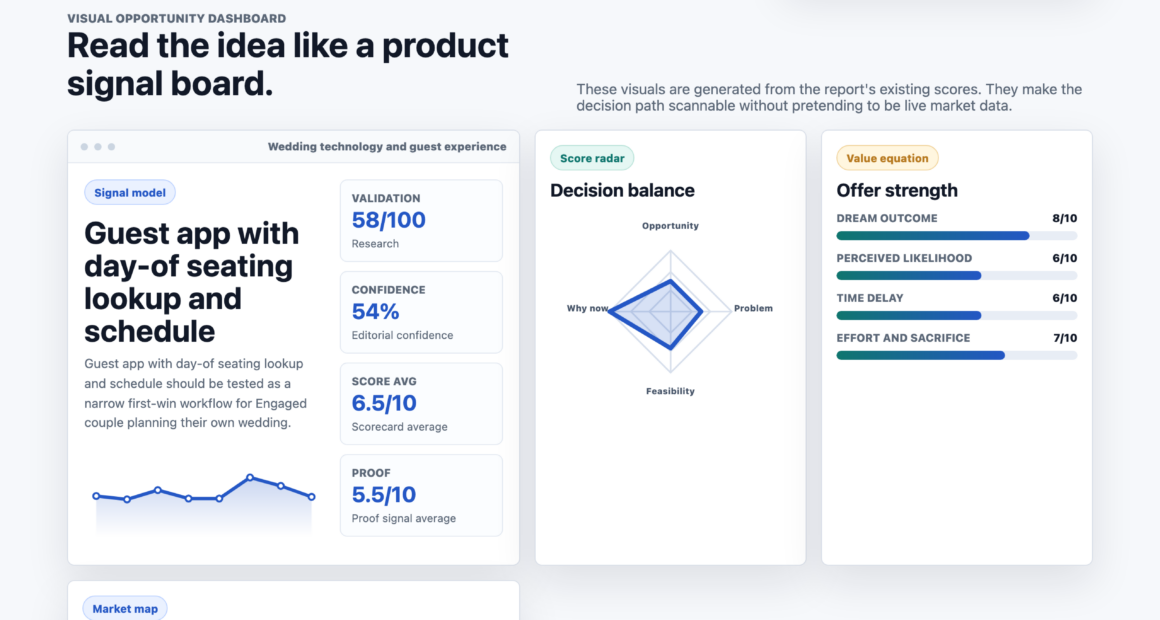
Guest app with day-of seating lookup and schedule
A new guest app allows wedding guests to view their seating and schedule via a shareable link, aiming to reduce logistical questions for couples on their wedding day.
RHEO · fluid lab
Thorsten Meyer AI published RHEO · fluid lab, a browser-based interactive fluid experiment with simple drag controls.
How to Think About the Best 10GbE Switch for an AI Lab
Meta description: “Many factors influence choosing the best 10GbE switch for an AI lab, and understanding them is key to making the right decision—continue reading to discover more.